Cloud Data Security in 2026: Risks, Challenges, and Best Practices
Cloud adoption has grown rapidly, but security has not always kept up. Many organizations now store a large share of their business data in the cloud, often across multiple platforms.
More than 60% of corporate data already sits in the cloud, and this share keeps growing. Securing it across multiple cloud platforms is difficult, especially when teams lack clear visibility and consistent controls. The cost of mistakes is high. In 2026, the average cost of a data breach reached $4.4 million, according to IBM, making cloud data security a critical priority for organizations.
Cloud providers operate under a shared responsibility model. While they secure the underlying infrastructure, organizations are responsible for protecting their own data. This makes cloud data security essential. Principles such as confidentiality, integrity, and availability help ensure cloud data protection, reliability, and accessibility.
This blog covers what cloud data security is, why it matters, the key challenges, major threats in 2026, and the solutions organizations can use to protect cloud data.
Cloud data security means protecting data once it moves to the cloud. People still need to use the data for daily work, but it should not be easy for the wrong users to access or for it to be exposed by mistake.
It applies to data stored in the cloud, such as files and databases, and data moving between systems, applications, and users. Most security issues do not come from complex attacks. They usually occur due to simple issues such as incorrect permissions, weak access controls, or basic human errors.
The cloud makes work easier in many ways. Teams can work from anywhere, systems can scale as needed, and operations become faster. Even so, many organizations hesitate to move sensitive or critical data because they are unsure how to properly secure it.
These concerns increase in multi-cloud environments. Data is spread across different platforms, tools work differently, and visibility becomes limited. During cloud migration, data moves more often, which increases risk. Simple access rules, basic monitoring, and clear security controls help reduce these risks and keep data safe.
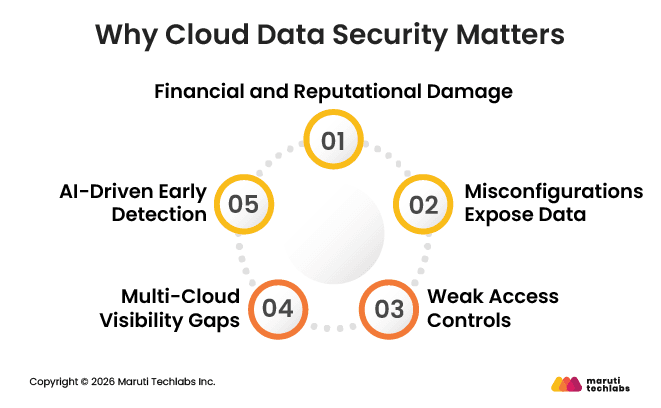
Cloud data security matters because when data is exposed, the damage is real and often long-lasting. It affects money, trust, and the business itself. And in many cases, the root cause is not a sophisticated attack, but simple mistakes.
As organizations move data and applications out of traditional data centers and into the cloud, security becomes harder to manage. Many familiar security practices still apply, but they need to be adjusted for cloud and hybrid environments. Below are some of the most common challenges teams face.
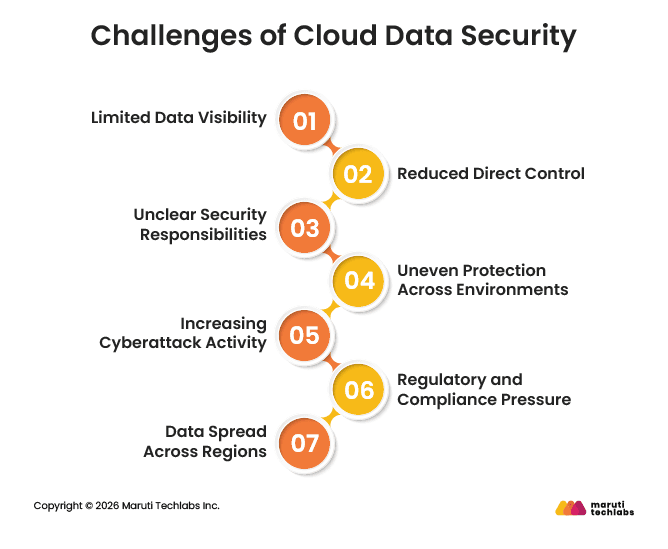
In cloud environments, teams often lack a clear view of where all their data and applications are stored. Data can be spread across accounts, regions, and services, making it difficult to track assets and identify risks.
When data and applications are hosted on cloud platforms, organizations no longer control the underlying infrastructure. This limits their control over access, configuration, and data sharing, increasing their dependence on the cloud provider's settings.
Cloud security follows a shared responsibility model, but roles are not always well understood. When teams are unclear about what they are responsible for versus what the provider handles, security gaps can easily appear.
Many businesses use a mix of cloud providers and on-premises systems. Each platform offers different security features, which can lead to uneven protection and inconsistent security policies across environments.
Cloud data stores are attractive targets for attackers. As organizations continue to learn how to manage data securely in the cloud, missteps and weak configurations create opportunities for breaches.
Data protection and privacy regulations are becoming stricter. Meeting compliance requirements across multiple cloud environments is challenging and requires strong policies, monitoring, and clear governance.
Cloud platforms often store data across global locations to improve performance. While this adds flexibility, it can raise concerns around data residency and sovereignty that are easier to manage in traditional data centers.
As cloud usage continues to grow, so do the risks tied to storing and managing data in cloud environments. While cloud platforms offer strong security features, most incidents occur due to basic configuration, access, or monitoring gaps.
These threats are expected to remain a concern in 2026 as cloud environments become larger and more complex.
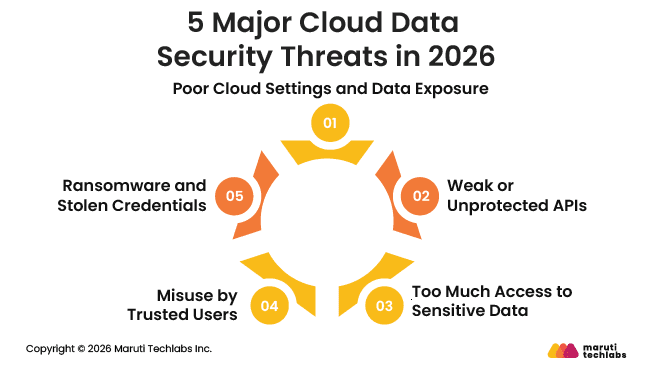
One of the most common cloud data security threats is incorrect configuration. Simple mistakes, such as open storage buckets, weak access controls, or missing encryption, can expose sensitive data. Attackers often look for these easy entry points rather than trying advanced techniques.
APIs play a key role in cloud environments by allowing applications to share data and communicate with one another. If APIs are not secured properly, they can become a direct path to sensitive information. Poor authentication, lack of monitoring, or outdated API versions increase the risk of data leaks and unauthorized access.
As cloud applications grow, the number of APIs also increases, making this threat harder to manage.
The ease of access offered by the cloud can quickly turn into a risk. When users are given more access than they need, sensitive data becomes easier to expose or misuse. This includes privileged accounts that are not regularly reviewed or removed.
In many cases, employees accidentally share data or change settings without realizing the security impact.
Not all threats come from outside the organization. Employees, contractors, or partners with legitimate access may misuse cloud data, intentionally or unintentionally. The cloud makes it easier to access data from anywhere, increasing the risk when access controls are weak or poorly monitored.
Credential-based attacks continue to rise. Attackers use phishing or leaked passwords to gain access to cloud accounts. Once inside, they may encrypt data, delete backups, or demand ransom. As cloud data becomes more valuable, these attacks are expected to increase in 2026.
Protecting data in the cloud starts with a few core ideas. Data should remain private, accurate, and available when teams need it. These basics guide the application of cloud data security solutions in real environments. The goal is not to add complexity, but to reduce risk while keeping systems usable.
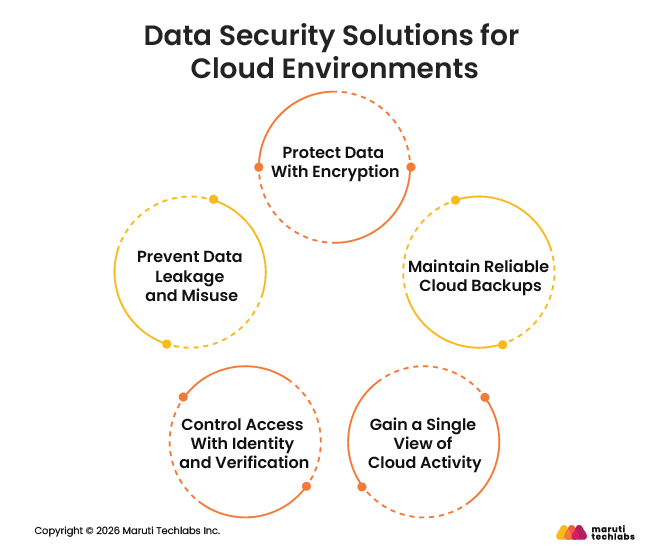
Encryption helps keep cloud data private. Data should be encrypted when it is stored in the cloud and when it moves between systems. If data is intercepted or accessed without permission, encryption makes it unreadable without the correct key.
Backups protect data availability. Even when data already lives in the cloud, it should be backed up separately. Many organizations use cloud-to-cloud backups to copy data to another cloud environment. This helps ensure data can be recovered if systems fail, data is deleted, or an attack occurs.
Security teams need clear visibility into what is happening across their cloud environments. A unified view makes it easier to spot misconfigurations, unusual activity, or weak controls. Without visibility, risks can go unnoticed for long periods.
Limiting who can access cloud data is critical. Identity and access management help ensure users only have access to the data they need. Multi-factor authentication adds another layer of protection by verifying user identity before access is granted.
Data loss prevention tools help monitor how data is used and shared. These tools can detect risky behavior, block unauthorized transfers, and reduce the chance of sensitive data leaving the environment unintentionally or through misuse.
Cloud data security plays a key role in protecting sensitive information and reducing the risk of ransomware and data leaks. As more business data moves to the cloud, having the right security controls in place is no longer optional; it’s a basic requirement.
That said, there is no single solution that works for everyone. The right cloud data security setup depends on your organization’s size, data types, compliance needs, and cloud environment. What matters most is choosing a solution that fits your existing workflows and can grow as your cloud usage expands.
To support this need, Maruti Techlabs has recently introduced a dedicated Cloud Security service. This new offering is designed to help businesses gain better visibility, reduce misconfigurations, and protect data across cloud environments.
If you’re looking to strengthen your cloud security strategy, explore Maruti Techlabs’ Cloud Data Security Services or contact us to discuss how our new cloud security solutions can support your business goals.
Cloud data security is about keeping data safe when it is stored, used, or shared in the cloud. It focuses on controlling access, encrypting data, monitoring activity, and preventing leaks, misuse, or loss—whether data is at rest, in transit, or being processed.
Cloud data security is a shared responsibility. Cloud providers secure the infrastructure, while organizations are responsible for their data, access controls, configurations, and usage. Most data breaches happen due to customer-side mistakes, not cloud provider failures.
DSPM helps by showing where sensitive data lives, who can access it, and how it is used. It finds risky permissions, exposed data, and forgotten assets. This visibility helps teams fix issues early before data is leaked or misused.
Start with strong identity controls and limit access to only what is needed. Encrypt sensitive data, enable logging, and continuously monitor activity. Review permissions regularly, secure backups, and fix misconfigurations early. Cloud security improves through steady checks, not a one-time setup.
There is no single best tool. Most organizations use a mix of identity management, encryption, monitoring, and data security tools. The right choice depends on your cloud setup, data sensitivity, and scale. Visibility, automation, and ease of use matter most.


